loading…
ZAP Server
FreeSafe, self-hosted OWASP ZAP operator for guided AI security scans, findings, and reports. Requires a separately running OWASP ZAP daemon.
About
Safe, self-hosted OWASP ZAP operator for guided AI security scans, findings, and reports. Requires a separately running OWASP ZAP daemon.
README

MCP ZAP Server
Give AI agents a safe, self-hosted OWASP ZAP operator for guided web security scans, findings, reports, and production guardrails.




Note This project is not affiliated with or endorsed by OWASP or the OWASP ZAP project. It is an independent implementation.
mcp-zap-server exposes OWASP ZAP through MCP over streamable HTTP so agentic tools can run operator-controlled security workflows without brittle glue scripts or unsafe scanner access.
Use it when you want:
- safe agentic scanning with guided defaults for spider, active scan, passive scan, API imports, findings, and reports
- operator control through API-key or JWT auth, tool scopes, runtime policy bundles, rate limits, and audit events
- self-hosted deployment with Docker Compose for local adoption and Helm for Kubernetes
- expert ZAP access when you intentionally need lower-level ZAP context, user, scan, and report controls
Full documentation: danieltse.org/mcp-zap-server
Watch the demo: browser demo or YouTube
Quick Start
Prerequisites:
- Docker 20.10+
- Docker Compose v2 (
docker compose) - an MCP-capable client, or the bundled Open WebUI client
git clone https://github.com/dtkmn/mcp-zap-server.git
cd mcp-zap-server
cp .env.example .env
# Generate values for ZAP_API_KEY and MCP_API_KEY, then put them in .env.
openssl rand -hex 32
openssl rand -hex 32
docker compose up -d
Then open:
- Open WebUI:
http://localhost:3000 - MCP endpoint for host-side clients:
http://localhost:7456/mcp
The default Compose stack publishes host ports on 127.0.0.1 only. Set MCP_ZAP_BIND_ADDRESS=0.0.0.0 only when you intentionally expose the stack behind trusted network controls.
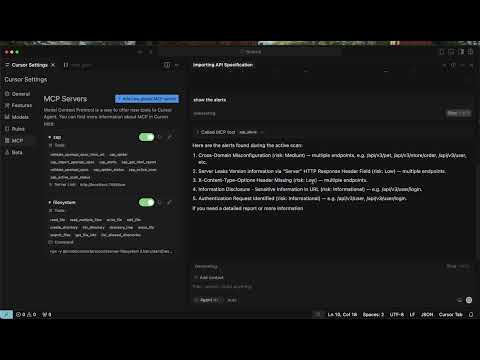
Client setup:
Discovery Metadata
This repository includes MCP Registry metadata in .mcp/server.json. The v0.8.0 Docker images are labeled with the MCP server name expected by registry and catalog tooling.
Docker Compose remains the easiest installation path because the MCP server is designed to operate with an OWASP ZAP sidecar and explicit auth keys. The OCI package metadata is for advanced standalone installs where OWASP ZAP is already running and reachable from the MCP container.
What You Get
- Guided scans: intent-first tools for spider, active scan, passive scan, API imports, findings, reports, and scan history.
- Expert ZAP control: optional lower-level tools for advanced ZAP context, user, scan, and report workflows.
- Authentication: API key mode by default, optional JWT mode with refresh and revocation support.
- Runtime policy bundles: dry-run and enforcement support through
zap_policy_dry_runand policy-mode configuration. - Scan queue and history: queued active, spider, and AJAX Spider jobs with claim-based recovery, durable Postgres state, and evidence export.
- Extension contracts: experimental policy, protection, evidence metadata, and extension metadata APIs with sample extension packaging.
- Operational guardrails: request body limits, rate limits, workspace quotas, tool-scope authorization, structured logs, metrics, and audit events.
- Deployment paths: local Docker Compose, production-oriented Compose, and Helm charts for Kubernetes.
Latest Release
v0.8.0 adds:
- public-preview extension API publication and standalone extension examples
- scan history release-evidence and customer-handoff tools
- HA queue claim fencing, dispatcher/result-applier boundaries, and Postgres race coverage
- Docker image packaging hardening, MCP Docker catalog labeling, and native-image port alignment
- MCP Registry metadata and agent install notes for marketplace discovery
Read the full notes:
Security Defaults
The default posture is intentionally conservative:
api-keymode is the base runtime default.nonemode is for explicit local dev/test only.- Docker Compose binds published ports to loopback by default.
- URL validation blocks localhost, private networks, and link-local targets by default.
- Guided auth uses credential reference allowlisting for server-side secrets.
- Public auth exchange endpoints are rate-limited.
- MCP request bodies have a hard early size cap.
Production and shared deployments should review:
- Security Modes
- JWT Authentication
- Authenticated Scanning Best Practices
- Abuse Protection
- Production Readiness Checklist
- Security Policy
Architecture
flowchart LR
Client["Open WebUI / MCP Client"] -->|"MCP over Streamable HTTP"| MCP["MCP ZAP Server"]
MCP -->|"ZAP API"| ZAP["OWASP ZAP"]
ZAP -->|"scan"| Target["Authorized target app"]
MCP -->|"reports / findings / history"| Evidence["Evidence + reports"]
For multi-replica queueing, durable Postgres state, claim recovery, and ingress affinity, use the operations docs instead of this README:
Extension Model
ZAP is the first scanner engine, not the whole product boundary. The current public extension work is intentionally small:
mcp-zap-extension-apipackages selected policy, protection, evidence, and metadata contracts without core runtime internals.- How extensions work explains the core versus extension boundary.
- Build your own extension shows the target standalone repository shape.
- Extension API release policy explains publication stages and compatibility gates.
- Standalone sample extension proves a separate project can compile against the API artifact.
This is not runtime multi-engine support yet. Additional scanner engines need an adapter design and explicit fail-closed capability boundaries before they become product claims.
Documentation Map
Start here:
- Full documentation
- OSS Extension Model
- Authentication Quick Start
- MCP Client Authentication
- Tool Surfaces
Scanning:
Operations:
- Runtime Policy Bundles
- Observability
- Production Checklist
- Release Evidence Handoff
- Native Image Performance
Open Source Core And Extension Model
mcp-zap-server is the Apache-2.0-licensed open-source core. It is intended to be useful on its own for self-hosted MCP and OWASP ZAP workflows.
Private or enterprise capabilities may be built as separate extensions around this core. Those extensions are not required to run the OSS project, and enterprise implementation code is not shipped in this repository.
The boundary is intentional:
- this repository remains the public OSS distribution
- extension points should be documented and kept stable where practical
- private extensions must not weaken the security, licensing, or usability of the OSS core
- security scanning and open-source program entitlements for this repository apply only to this public project
Contributing And Support
If this project saves you time or becomes part of your security workflow, you can sponsor the maintainer to support ongoing maintenance.
Agentic Lab offers optional paid support for teams adopting the public core in production. Commercial support is separate from the Apache-2.0-licensed OSS distribution, and the public core should remain usable without private extensions or paid services.
License
Apache License 2.0. Copyright 2025-2026 Daniel Tse. See LICENSE.
How to install
Add this to claude_desktop_config.json and restart Claude Desktop.
{
"mcpServers": {
"mcp-zap-server": {
"command": "npx",
"args": []
}
}
}

